Protection from ransomware

Ransomware has been in the headlines of every major newspaper lately. According to research, ransomware has become the most dangerous malware, and many of today’s businesses aren’t prepared to handle it.
Ransomware isn’t a one-size-fits-all type of threat; it comes in many different shapes and sizes, from lockers that encrypt files on your computer to the infamous WannaCry virus, which locked down computers around the world and demanded money from their owners for release.
Growing threat of ransomware
Ransomware is a type of malicious software that blocks access to user data or threatens to publish it online. Victims are typically given some sort of window of time to pay up or lose their data permanently.
Ransomware has existed for several years, but it has become much more prevalent in recent years.
With almost 4,000 new families being released last year alone, ransomware continues to be a growing threat on both small and large businesses around the world.
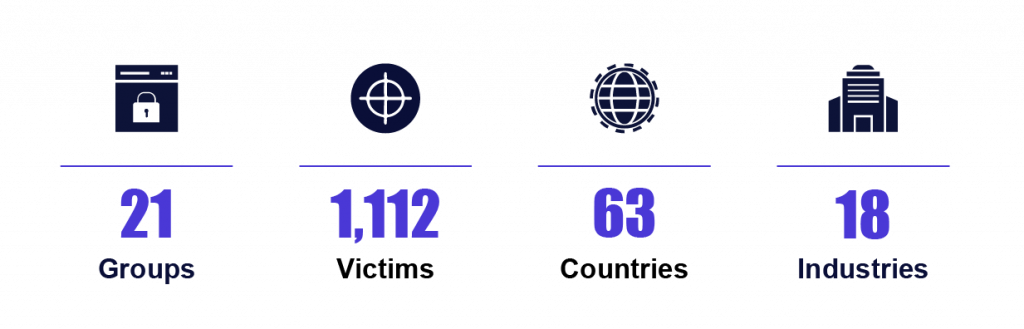
These attacks happened in 2021 alone!
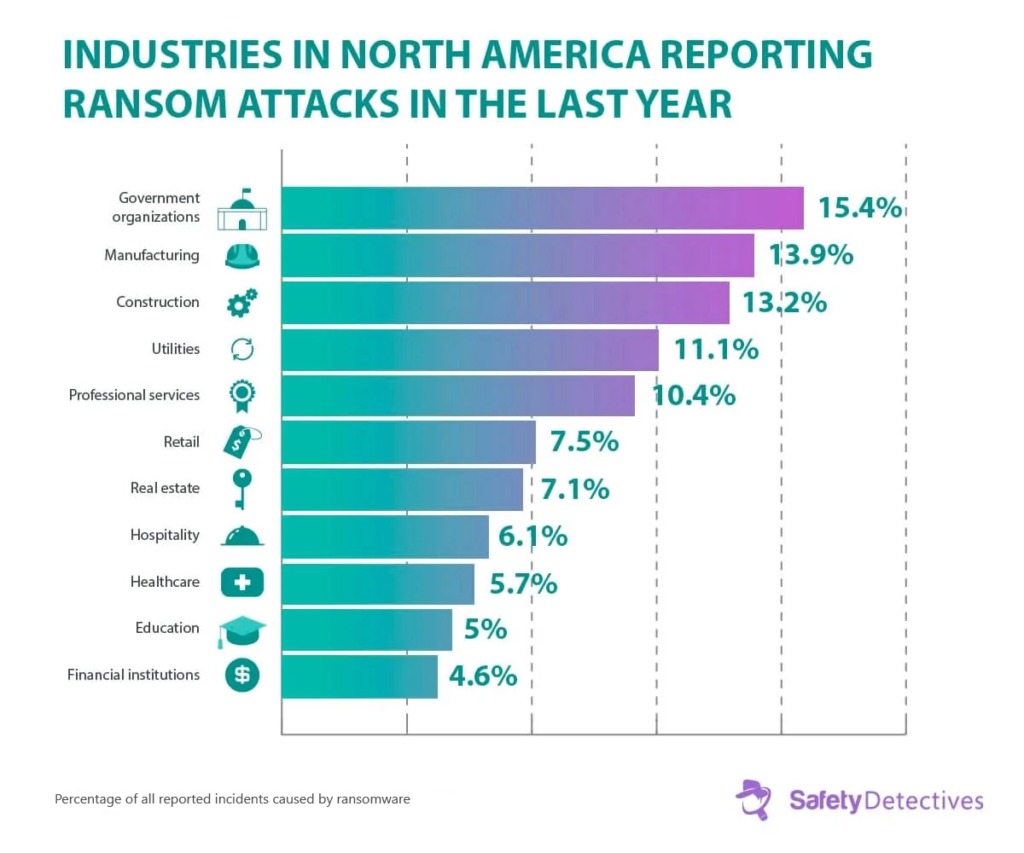
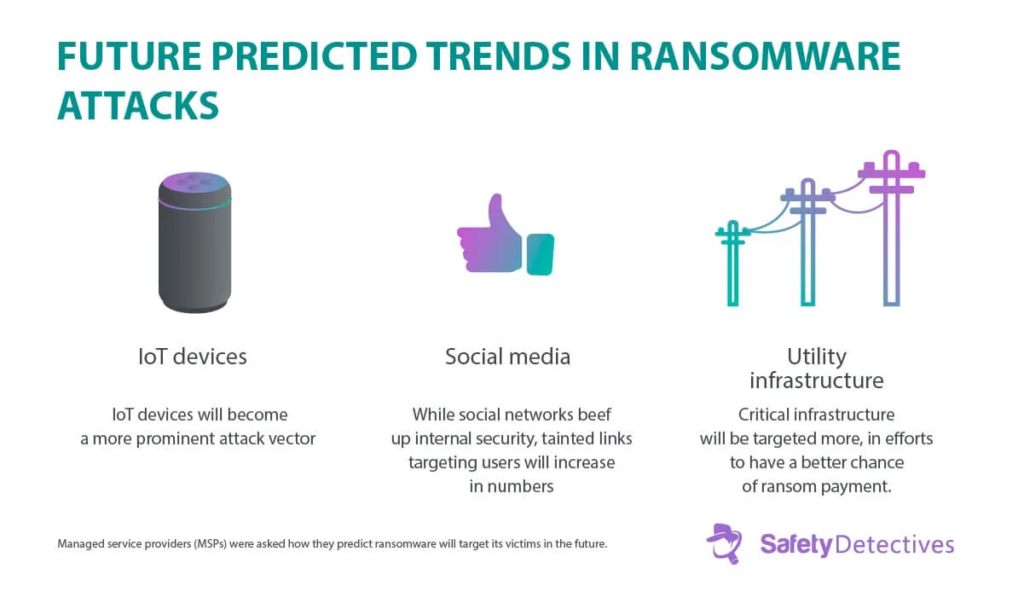
Ransomware is predicted to grow at an alarming rate and penetrate many sectors of the economy. That makes it even more dangerous. It will be able to affect critical infrastructure and people’s homes. Industrial ransomware already hit hospitals, power grids and oil infrastructure several times in 2021-22 in the US alone.
The importance of information security
Losing important data can be a nightmare for a small business, but it’s not an inevitability. The only way to prevent a full-blown catastrophe is through information security measures. In most cases, all you need to do is make backups of your files and perform regular updates of computer software.
Define Threat Vectors
In order to protect yourself against certain types of attacks, it’s important to first understand what a threat vector is. A threat vector can be defined as a possible entry point for an attack. This could be anything from a phishing scam, through to an exploit that takes advantage of a vulnerability in outdated software. Every company needs to know what its threat vectors are and how they might compromise security.
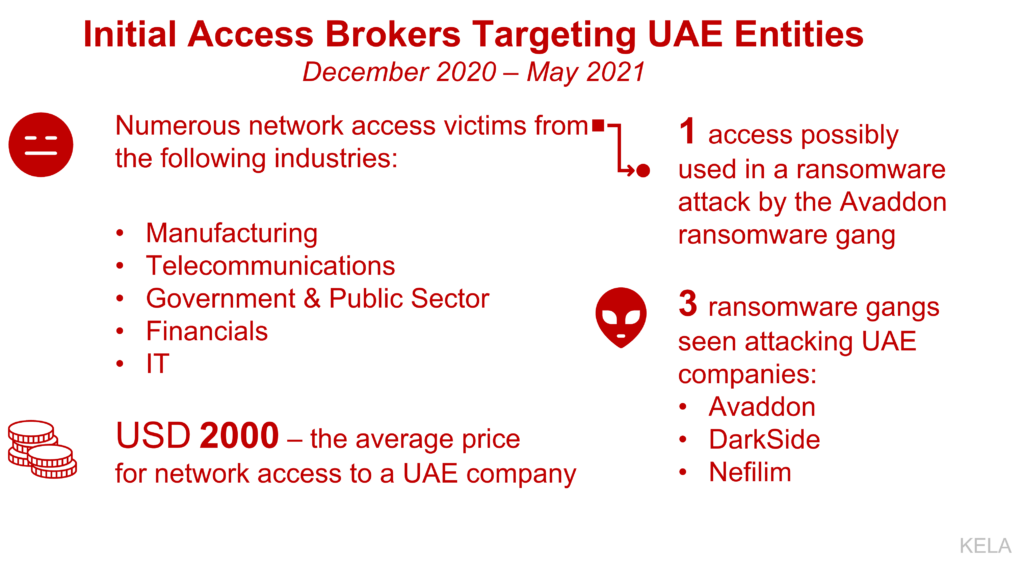
Knowing these points means that you can either strengthen or mitigate them before any damage is done. For example, if there were only one threat vector for an organization it would likely be email; however nowadays more people tend to use instant messaging platforms like WhatsApp over email. Besides, hackers even sell prepared access paths to various breached victims to anyone for relatively low prices in their online stores on the Dark Web.
While you may not have control over all potential points of contact with your customers, there are some standard ways around mitigating risk.
Two-factor authentication when customers log in from new locations, whether physically or online is one of the best ways to limit access. Another way is through training employees on how to spot suspicious messages. This stops even well-known tactics such as phishing scams from taking hold in your business. Despite working hard to make sure all of your staff and customers know about cyber threats and how to avoid them, there will always be unknowns that mean you need further protection.
Employing a full-time IT professional, no matter what size your company is, is another great security measure that would help ensure that most threat vectors have been considered and mitigated.
Further Steps
At Roman Consulting, we’re experts in information security. We know how to keep information safe, and that’s just what we do for medium and small businesses globally. Cybersecurity is our specialty—and because there are many different aspects to keeping a company secure, it’s worth taking advantage of our expertise.
From checking for malware on your network to administering regular cybersecurity audits, there are several ways that Roman Consulting can protect you against these destructive attacks.
There are many measures you should use in order to protect your company against getting infected by any kind of malware, but they all boil down to three kinds: proactive measures, reactive measures and information security awareness. Regardless of your size, you should implement these kinds within your organization.
The first measure is all about increasing your IT resilience through having at least one redundant backup system that allows you to continue working when something happens to the main computer systems—this also reduces or removes downtime caused by other means than ransomware infections, e.g., outages, regular maintenance or data corruption. We can provide you with comprehensive programs for operational backups on premises as well as in the cloud which allow you to minimize risks while saving time and money.
If a threat does arise, you need a clear protocol for response so your entire team knows what actions to take under different circumstances. We have implemented countless automatic monitoring solutions, so you are always one step ahead when it comes to detecting threats early on before they have a chance of spreading throughout an entire network, putting everyone at risk. This significantly increases your chances of recovering without paying ransom, or even better—without any damage done to your system whatsoever.
Finally, there’s awareness. We believe every employee has a part to play when it comes to information security, but just like proper education is required for effective security tools and backups, you need proper training in order to leverage information security properly.
